Enterprise transformation is no longer a one-time modernization effort. It is a continuous operating-model shift shaped by cloud migration, hybrid work, AI-driven productivity, and increasingly sophisticated cyber threats. The real challenge for organizations today is not simply adopting new platforms — it is aligning identity, governance, automation, security, and people into a cohesive system.
Nikolay Milyaev, Senior Architect at Microsoft Consulting Services, has spent more than two decades navigating this evolution. Having led over 50 enterprise-scale transformation projects across global organizations, he works at the intersection of Zero Trust architecture, endpoint modernization, integrated XDR security, and AI-enabled operations.
In this comprehensive conversation, he shares lessons from cloud migrations, common executive missteps, the growing cybersecurity risks amplified by AI, and what truly defines a future-ready enterprise.
1. You’ve spent more than 19 years at Microsoft Consulting Services. What major shifts in enterprise technology have most defined your career since you started?
Nikolay Milyaev:
Disclaimer: Everything I discuss today reflects my personal perspective and experience and should not be taken as an official statement from Microsoft.
Two major waves have shaped my career.
I’ve been with Microsoft Consulting Services for over 19 years now, and two major waves really stand out when I look back.
The first was the big migration from classic on-premises, project-by-project IT to cloud and hybrid services. When I started, we were still building and maintaining infrastructure the old way. Then clients began moving core workloads to Azure and Microsoft 365, and everything changed. The center of gravity shifted to identity, automation, and continuous operations. My work moved from configuring server monitoring and management and writing scripts to helping enterprises modernize to cloud endpoint management, secure access at scale, and run standardized, policy-driven environments with real telemetry and DevOps-style delivery.
The second wave — the one we’re riding right now — is AI. We’ve gone from tools that simply generate reports to systems that actually assist decision-making, automate routine security and operations tasks, and reshape how teams work every day. For me, the real focus is applying AI safely: accelerating investigations and response, strengthening detection and posture management, and removing friction for users — all while keeping governance, data protection, and Zero Trust principles.
2. Having led over 50 enterprise projects across global organizations, what common challenges do companies face when undergoing large-scale digital transformation?
Nikolay Milyaev:
After 50-plus transformations, I can tell you the hardest parts are almost never the technology itself. It’s the operating model, governance, and getting it right for the people at the end of the line.
The biggest issue I see is identity and access finally becoming the real perimeter. Companies move workloads to the cloud but hang on to legacy authentication, patchy Conditional Access, and weak device trust. That creates friction, security holes, and a mountain of exceptions. Getting to a clean Zero Trust baseline — strong identity, MFA or passwordless authentication, and policy-driven access — is usually the turning point. Even today, I still walk into customers where MFA isn’t fully rolled out everywhere, and we roll up our sleeves to close those gaps.
Second is the gap between the nice architecture diagrams and the real endpoint estate. At enterprise scale, you always have Windows 10/11, servers, AVD, legacy apps, third-party agents, and devices that aren’t fully managed. The challenge is building a repeatable management and security posture with Intune, Defender telemetry, clear deployment rings, and measurable health signals instead of “best-effort” firefighting.
Third, governance and data control always lag behind shiny new capabilities. Organizations adopt Microsoft 365, cloud services, and now AI features quickly, but Purview, DLP, information protection, logging, and proper role-based access aren’t aligned. Risk builds quietly until an audit or incident forces a reset. A lot of customers aren’t even using everything they’ve already licensed simply because configuration and implementation are complex. We spend a good part of every engagement helping them unlock what they already own.
3. From your experience, what separates organizations that successfully adopt cloud technologies from those that struggle?
Nikolay Milyaev:
It’s not how fast they migrate — it’s whether they actually change how they run IT.
The successful ones treat cloud as an operating-model shift from day one. They standardize landing zones, identity, networking, policy, and logging early so every new workload follows the same repeatable pattern. The ones that struggle still treat Azure like “just another datacenter” and end up rebuilding their old habits with newer tools.
Another clear separator is building security and governance in from the start, not bolting it on later. The winners start with Zero Trust fundamentals — strong identity, Conditional Access, device compliance, least privilege, and central visibility through Defender and SIEM. The others delay it, then drown in exceptions and reactive firefighting.
Automation and measurement matter hugely too. Strong organizations use rings, structured deployment pipelines, Infrastructure as Code where it fits, and they track real outcome metrics: device health, patch compliance, vulnerability exposure, MTTR, and service reliability. The weaker ones still do manual deployments and measure success by “migration complete” rather than better operations.
Finally, it comes down to people and alignment. Clear ownership across security, identity, endpoint, and platform teams, realistic scope, and real investment in upskilling make all the difference. When accountability is fuzzy and priorities compete, you see cost overruns, support headaches, and security gaps later.
4. Endpoint management has become more complex with hybrid work environments. How have solutions like Intune and Autopilot changed the way companies manage devices today?
Nikolay Milyaev:
Intune and Autopilot have completely flipped endpoint management from “imaging and touching PCs” to “policy and provisioning as a service.”
Autopilot changes the whole starting point. Instead of IT physically handling devices, loading thick images, and spending hours on post-configuration, you can ship a laptop straight from the OEM to the user’s home. They power it on, sign in with their corporate credentials, and the device auto-enrolls, applies apps, policies, and security baselines. I just helped a global company migrate to a new tenant — devices arrived ready-made at people’s houses. They turned them on, entered their login, and were productive in minutes. Ten years ago, that scenario was impossible.
Intune itself moved us from a network-bound, VPN-heavy model to true internet-first management. You control Windows, macOS, and mobile devices through one pane of glass — compliance policies, security baselines, update rings, and Endpoint Privilege Management so users don’t run as permanent admins.
The biggest shift is how security and management have merged. Intune plus Defender for Endpoint lets device health and risk signals feed directly into Conditional Access. Access is no longer just about username and password; it’s based on real-time posture. You move from “we deployed antivirus” to continuous vulnerability management, attack-surface reduction, and automated response.
It’s not necessarily simpler than the old world, but it is far more scalable and actually matches hybrid work. The organizations that win treat Intune and Autopilot as a full modern device lifecycle — procurement through provisioning, protection, and retirement — with standardization, rings, and measurable outcomes.
5. You specialize in enterprise security. How would you describe the biggest cybersecurity risks organizations underestimate right now?
Nikolay Milyaev:
Right now, I believe many organizations are still underestimating how AI tilts the economics in the attacker’s favor.
Even 10–15 years ago, I lived through incidents where a customer’s entire datacenter was wiped out because protections weren’t in place. We had to rebuild everything from scratch and produce stacks of security architecture documents. Those lessons stay with you.
Today, AI makes attacks that once needed time, language skills, and manual effort scalable and semi-automated. Phishing and social engineering can be generated faster, in better English, tailored to an industry, and refined based on what lands. Commodity attacks become more effective and far higher in volume.
On targeted attacks, AI is frighteningly good at reconnaissance — pulling org charts, public documents, meeting notes, email styles, and supplier relationships. It crafts highly convincing pretexts: fake vendor invoices, “CEO-style” urgent requests, or helpdesk messages that match internal processes exactly.
We also can’t ignore the dual-use risk inside the organization itself. If governance around AI tools is weak — over-broad access, poor data classification, and loose plugin controls — attackers (or even insiders) can abuse the very AI capabilities you paid for.
My practical takeaway after two decades in the field: the defensive answer is still classic Zero Trust fundamentals plus AI-era controls. Strong identity and Conditional Access, least privilege, tight governance of AI data access, proper classification and DLP, and security operations that can actually use Defender/XDR telemetry to respond at speed. AI doesn’t replace the basics — it punishes anyone who never operated them.
6. With the rise of integrated security platforms like Microsoft Defender and XDR, how should companies rethink their overall security strategy?
Nikolay Milyaev:
Integrated platforms like Microsoft Defender and XDR force a fundamental shift: from a collection of separate tools to one holistic, end-to-end system.
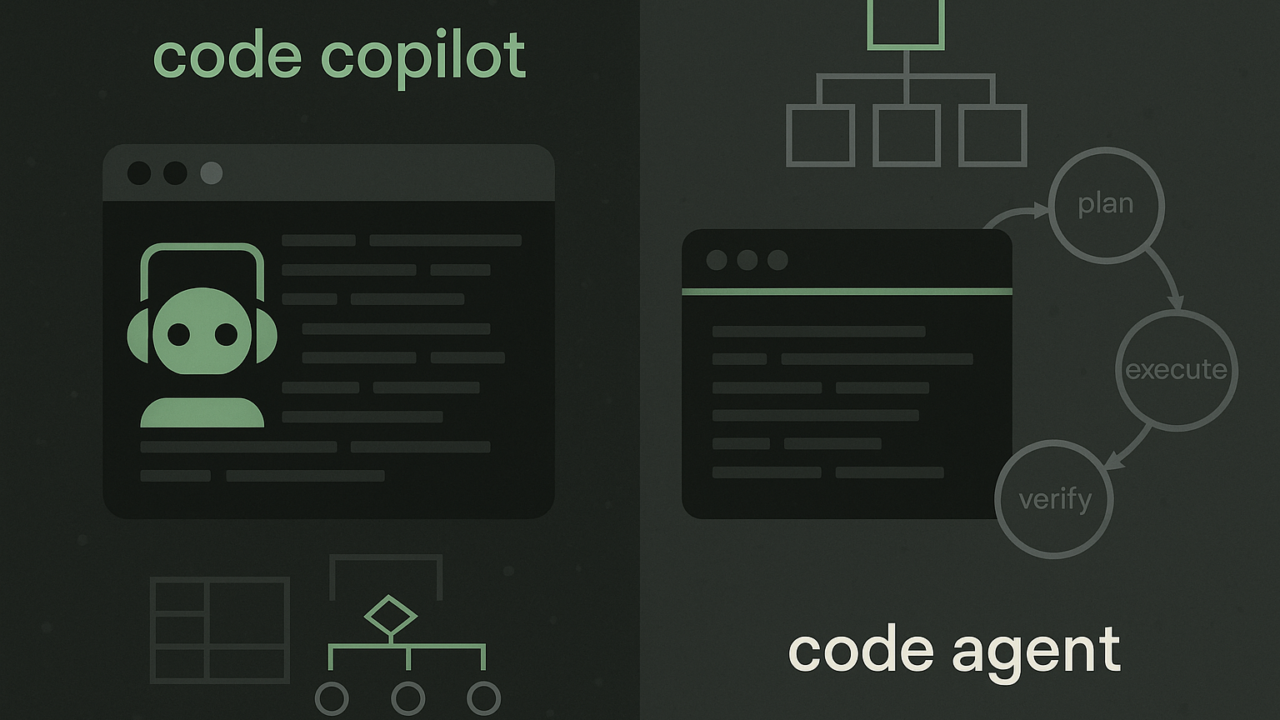
You have to assume protection is needed at every layer — identity, endpoints, email, collaboration, cloud apps, data, and infrastructure. The power of XDR is that it correlates signals across all those layers so you stop chasing isolated alerts and start seeing the full attack story.
That changes security operations too. Instead of manual triage on every alert, you build a pipeline where signals are normalized, enriched, prioritized, and then AI and automation handle routine responses — isolating devices, blocking sign-ins, and kicking off investigations. Analysts focus on the hard stuff: oversight, exceptions, and complex decisions.
Strategically, it means three things. First, invest in signal quality and coverage — close blind spots and ensure consistent telemetry in hybrid environments. Second, make identity and device trust your real control plane so Conditional Access and risk policies can act in real time. Third, build operational maturity — playbooks, clear roles, tuning, incident response, and metrics that actually matter (time to detect, time to contain).
The goal isn’t “AI replaces people.” It’s AI handling speed and scale while humans stay responsible for governance, risk decisions, and continuously improving the system.
7. Many companies are moving toward Azure and Windows 365. What are the most common misconceptions you encounter during cloud adoption projects?
Nikolay Milyaev:
The most common misconception I still hear is that cloud is simply “someone else’s datacenter,” so people try to run Azure and Windows 365 exactly the way they ran on-premises.
You see it in the designs: teams keep legacy network dependency and perimeter thinking instead of building around identity, device trust, and internet-first access. They lift and shift without proper landing zones, policy, or automation, then wonder why costs and complexity go up. They also expect provisioning to work like the old imaging and domain-join world instead of modern Autopilot and compliance-based models.
The organizations that succeed accept early that cloud changes the operating model. They standardize, automate, design for continuous operations and telemetry, and bake governance and security into the foundation instead of adding them later.
8. As you are working closely with executives, how do you align technical solutions with business goals and measurable outcomes?
Nikolay Milyaev:
I always start by translating the business goal into three to five measurable outcomes, then work backward to the technical design.
With executives, the conversation is about risk, cost, productivity, and time-to-value. So I frame everything that way: “Which decision are we improving? Which failure mode are we reducing? What operational burden are we removing?” We agree on the metrics from day one — baseline and target.
In security projects, that’s usually time to detect and contain, reduction in high-risk exposures, compliant device percentage, critical patch latency, standing admin rights removed, and helpdesk tickets avoided. For endpoint or cloud workspace projects, it’s provisioning time, day-one user readiness, VPN dependency, session reliability, and cost per user.
From there, the roadmap is outcome-led, not feature-led: quick wins in a pilot ring, then scale with governance and automation. I keep trade-offs visible — stronger Conditional Access might add a bit of friction, so we define acceptable user experience and exception handling up front. Regular executive checkpoints review real metrics, unblock decisions, and adjust based on evidence, not opinions.
9. With AI tools like Copilot entering the enterprise space, how do you see AI reshaping productivity, security, and day-to-day operations?
Nikolay Milyaev:
AI is reshaping the enterprise in three tightly connected ways: how people actually produce work, how we manage risk, and how operations run day to day.
On productivity, tools like Copilot shift knowledge work from “create from scratch” to “iterate and decide.” People spend less time searching, summarizing, formatting, or writing first drafts and more time reviewing, refining, and making judgment calls. The organizations that get the biggest lift are the ones that give AI structure — templates, shared vocabulary, approved data sources — because AI amplifies whatever process you feed it.
On security, AI is a double-edged sword. Defenders gain speed in triaging alerts, correlating signals across identity, endpoint, email, and cloud, and reducing time to contain. But the governance challenge grows: what the AI can see, what it can act on, and how you prevent accidental oversharing. That pushes us harder toward Zero Trust plus strong information protection — sensitivity labels, DLP, least privilege, clear boundaries, and full auditability of AI interactions.
In day-to-day operations, AI moves us from manual tickets to machine-speed workflows. In IT and SecOps, I expect far more automated responses for common scenarios: isolating devices, disabling risky sign-ins, blocking indicators, generating change plans, and producing human-readable summaries. Humans stay in the loop for policy, exceptions, and risk decisions, but routine work becomes faster and more consistent.
Bottom line: AI isn’t just another feature you switch on. It’s an operating-model change. The winners treat the rollout like any production system — clear use cases, guardrails, measurement, and continuous tuning.
10. Based on your experience, what defines a truly future-ready organization in today’s rapidly evolving technology landscape?
Nikolay Milyaev:
A truly future-ready organization is one that can adapt faster than the environment changes without sacrificing security or reliability. It behaves like a frontier team: curious, experimental, and able to pivot based on evidence.
Its operating model is built for continuous change. Platforms are standardized, automation is the norm, and teams ship improvements regularly rather than treating transformation as a one-off project. Decisions are driven by telemetry and measurable outcomes, not assumptions.
Security is a core design principle, not a separate workstream. Identity is the control plane, least privilege is enforced everywhere, data is classified and governed, and the organization can respond quickly when threats or priorities shift.
These organizations actively experiment with AI as a real capability. They run structured pilots, find where it removes friction or improves decisions, and scale what works — always with guardrails: clear data boundaries, monitoring, and accountability.
Finally, they never stop investing in people. Skills development is continuous, and teams are encouraged to challenge old processes. In the end, the real competitive advantage isn’t any specific toolset. It’s the organization’s ability to keep learning, adapting, and staying operationally disciplined at the same time.
What Truly Defines Enterprise Resilience
Enterprise evolution is not defined by the number of tools deployed, but by how well those tools are integrated into a disciplined operating model.
Identity has become the control plane. Automation must replace reactive firefighting. Governance must lead innovation — not follow it. And AI must be implemented with measurable outcomes and strong guardrails.
The organizations that will thrive are those that adapt deliberately, securely, and continuously — without sacrificing resilience, trust, or accountability.