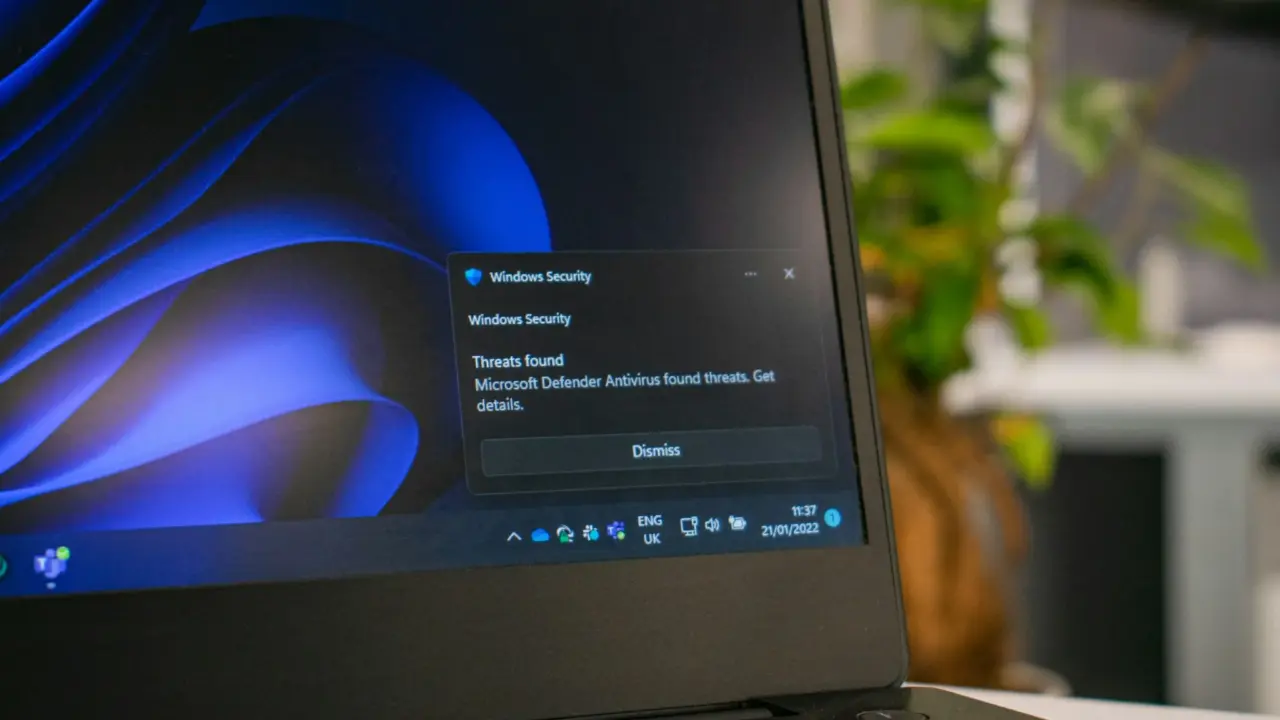
Hackers have already breached at least one organization by exploiting Windows security flaws that were made public before Microsoft fixed them.
The attackers are using three vulnerabilities called BlueHammer, UnDefend, and RedSun, which affect Microsoft’s built-in antivirus, Windows Defender.
These bugs can give attackers administrator access on vulnerable Windows computers, turning a debate over public disclosure into a real risk for companies that have not secured their systems.
A public exploit leak is now being used in real attacks
TechCrunch reported that Huntress researchers have seen these flaws being abused in real attacks over the past two weeks. This means the problem is no longer just theoretical or limited to online posts.
It is still unknown who was targeted or who the hackers are, but the attack seems to use code published online by a security researcher named Chaotic Eclipse.
This researcher released exploit code for all three bugs and suggested that disagreements with Microsoft were part of the reason for making the details public.
Only one of the three flaws has been patched so far
BlueHammer is the only one of the three bugs that Microsoft has fixed so far.
Microsoft’s advisory for CVE-2026-33825 addresses this flaw, which public records describe as an elevation-of-privilege issue in Microsoft Defender.
Huntress saw attackers using exploit code that was already available, showing the ongoing risk between public disclosure and complete protection.
This puts defenders in a tough spot. Even though Microsoft has fixed one flaw, exploit code for all three vulnerabilities is already out there and easy for others to use.
TechCrunch quoted Huntress researcher John Hammond, who said the exploits are now so easily available and already weaponized for easy use, making this another tug-of-war match between defenders and cybercriminals. He also said that situations like this force defenders to race against attackers who have ready-made attacker tooling.
Microsoft is defending coordinated disclosure, not public dumping
Microsoft did not go into detail about the technical disagreement. The company supports the usual industry practice of coordinated vulnerability disclosure.
Microsoft communications director Ben Hope said the company supports coordinated vulnerability disclosure, calling it a “widely adopted industry practice” that helps make sure issues are investigated and fixed before details are shared publicly.
This response highlights the bigger debate behind the situation. When researchers share exploit details before a patch is available, it is called full disclosure.
Sometimes this pushes vendors to act quickly, but it can also give criminals and state-backed hackers instant access to working attack code. In this case, the second risk happened first.
A warning for organizations still relying on default defenses
The main takeaway for businesses is clear but concerning: even built-in security tools can become targets if public flaws are not patched.
All three vulnerabilities affect Windows Defender, which many organizations use as their basic protection.
This makes the current attacks especially important, since the tool meant to stop intrusions is now helping attackers gain more control.
Right now, only BlueHammer has a Microsoft patch (CVE-2026-33825), but the bigger risk remains because exploit code for the other flaws is still out there.
Until those gaps are closed, organizations are facing real attack methods, not just theoretical Windows bugs.